Cloud security concerns are often misunderstood, due to the complex nature of cloud computing. Too often, businesses fail to understand what are the cloud application security issues and how to handle them, leaving them vulnerable to a variety of threats.
Due to the cloud's scalability, cloud application security issues have grown considerably. Not only that, but traditional security methods often fall short when it comes to application-level security in cloud computing.
94% of organizations have some degree of cloud security concern.
What’s more, 58% of organizations see unauthorized access as the top security danger, according to the 2022 Cloud Security study.
As businesses adapt to cloud computing models, understanding the intricacies of these connections is crucial to keeping data safe.
In this article, we will talk about what are the cloud application security issues in detail. So, let’s get started.
Related: Understanding SOA in cloud computing
What are the cloud application security issues?
The term ‘cloud application security’ refers to the practice of safeguarding cloud-based software applications from the start of development. It’s important to:
- Keep everything stored in the cloud
- Protect cloud-based apps from cyberattacks
- Restrict access to just the right people
There must be safeguards in place to prevent attacks on these cloud-based apps and to prevent unwanted access to the data they store. You will also need the same level of oversight and management with cloud applications you use.
Now that we know what cloud security is, we can examine the most pressing threats and the reasons why it's so important to guard against these security issues.
Types of cloud application security issues
Let’s focus on some of the most common security issues around cloud computing applications:
1. Misconfiguration
One of the most common causes of data breaches is improperly configured cloud infrastructure.
Misconfigurations in a company's cloud might leave sensitive data and programs open to cyber criminals.
It may be challenging for businesses to guarantee that only authorized users have access to their data stored in the cloud because of the infrastructure's open nature and emphasis on data sharing.
Having poor oversight or management of their cloud hosting infrastructure might make this problem even worse.
In a nutshell, the repercussions of misconfiguration threaten cloud security and may have a negative effect on daily operations for companies.
Those in charge of managing their company's cloud application should be well versed in the security tools in order to avoid accidental misconfigurations.
2. Data leakage or loss
One of cloud computing's primary advantages is the simplicity with which data can be shared and collaborated on by internal and external parties.
However, there are potential security issues and challenges in cloud computing due to the fact that transferring data in the cloud is typically done via:
- Direct email invitations
- The distribution of a public link to a specified group of users
The most prevalent security concern in cloud computing is the loss of data. When information is lost, it is either erased, corrupted, or rendered unusable by human action or automated processes.
Needless to say, loss of data — most especially customer data and intellectual property — is a prime concern for businesses.
3. Cyberattack
Cyberattackers know how to attack poorly protected cloud-based infrastructures.
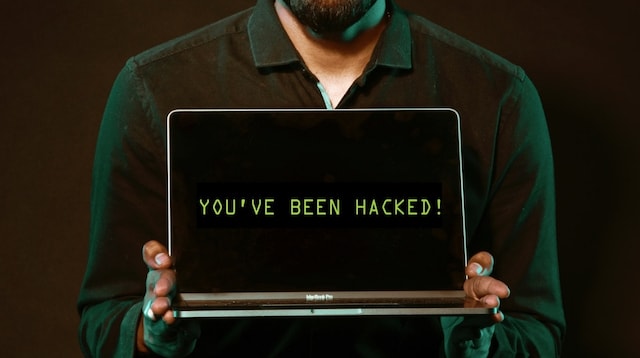
In May 2021, Air India had suffered a cyberattack where the personal details of about 4.5 million customers around the world were stolen, including passport, birth dates, names, and ticket information.
After the data breach, Air India was sued for Rs 30 lakh.
It is anticipated that this pattern of frequent devastating attacks will persist in the coming years.
If businesses are serious about preventing cyberattacks on their operations, they need to assess their vulnerability.
This can be done by conducting a variety of security checks, which will reveal vulnerabilities in the company's present cloud system.
To further improve the effectiveness of its cybersecurity solution, the company also should use solid cloud security strategies.
4. Insider threats
Do you know that cloud isn't the only place where an organization's network is vulnerable to threats? There is a thing called insider threats that prevails in many organizations.
It has been found that 30% of data breaches are caused by insiders.
It's harder to spot suspect threats if insiders are involved. Every company needs effective security mechanisms to detect dangerous insider behavior before it affects business operations.
There are two types of insider threats:
- Those that are deliberate, like a dissatisfied employee seeking retribution
- Those that are unintentional, like an employee who clicks on a malicious email link
Not only do we have employees, but we also have other insiders. Data may also be improperly accessed, exposed, or stolen by contractors, vendors, and partners.
The actions of both users and administrators, as well as the software being used, in cloud storage systems, are often hidden from view.
5. DDoS attacks
Malicious attacks against cloud service providers are on the rise as more companies and processes transition to the cloud. These days, distributed denial of service or DDoS attacks are more widespread.
The goal of a DDoS attack is to flood a website with so many fake requests that it can't handle the real ones. DDoS attacks can make a website inaccessible for many days.
This can cause a drop in sales, goodwill, and credibility associated with the business.
Most DDoS attacks are directed against the web servers of big institutions like:
- Banks
- Media outlets
- Government agencies
The intent of DDoS attackers is to cause disruption.
In order to access databases or servers, hackers use advanced persistent denial of service (APDoS), which targets bypassing the application layer.
Editor’s note: GoDaddy’s all in one website security tool comes with a firewall, automatic backups, an SSL Certificate and a malware scanner. The company's security experts are always just a call away.
6. Lack of compliance
Compliance rules and industry standards like GDPR, HIPAA, and PCI DSS are getting increasingly demanding as a consequence of the rising concern for data protection.

Monitoring who has access to data and what they do with that access is essential for maintaining compliance.
If adequate security measures (such as access restrictions) are not in place, it can be challenging to monitor data. Such lax behaviour normally invites cloud application security threats.
7. Insecure API
In today's cloud-based systems, APIs are often used for both internal and external data exchange. The problem is that hackers love to target APIs because they provide a wealth of features and data to exploit.
But wait, what exactly is API?
API (Application User Interface) is the key tool for controlling the system in a cloud environment. Because of its widespread availability, API poses a serious threat to cloud safety.
Sometimes the API setup is not up to standards, which can endanger cloud safety.
These are the most typical issues with application-level security in cloud computing:
- Insufficient monitoring
- Free and secret access with no authentication required
- Passwords and tokens can be reused
- The use of explicit messages for authentication
Hackers will uncover these loopholes and use them to bypass authentication procedures via APIs.
Hence, one should pay extra attention to application-level security in cloud computing. Protecting APIs and safeguarding API gateways should be a part of any risk management plan.
Related: Why you must institute two factor authentication now
Cloud application security in summary
Cloud computing offers a multitude of benefits to its users, including the facilitation of distant resource access, data sharing, and more.
Nevertheless, providing a high level of cloud security to battle typical cloud security threats is vital in order to avoid data loss and security breaches.
Risks to security can be minimized greatly with the right methods and practices. However, these safeguards cannot be installed quickly. Implementing them successfully calls for a well-thought-out strategy and expertise. You can collaborate with your cloud provider to create a thorough security plan.