A renowned Beachbody fitness instructor famous for exercise videos including PiYo, TurboJam and TurboFire, Chalene Johnson also is a best-selling author and successful entrepreneur who’s online tribe knows her as a social media superstar. She counts more than 482,000 followers on one of her Instagram accounts, has nearly a million Facebook fans and 102,000+ Twitter followers.
Chalene Johnson also is the survivor of a online security attack that cost her business hundreds of thousands of dollars — an experience that’s prompted her to fight back by raising awareness about cyber security.
“My story could be your story.” ~ Chalene Johnson, who was the victim of a complex social media hack
Chalene says she felt an obligation to share her story so it will be less likely to happen to others.
Chalene Johnson: How my social media accounts got hacked
In 2015 Chalene suffered a social media hack to her Instagram and Twitter accounts. By her estimate, the security breach cost her thousands of followers and more than $200,000!
She recalls a friend notifying her of the hack via text message, and she did what any of us would likely do — she changed her password. Just one problem: the hackers had already gained access to Chalene’s email. Every time she changed the password, the hackers got back into her email account. They began posting messages that taunted her. They posted porn and animal cruelty. They deleted photos and changed usernames.
Chalene felt helpless. Friends and business colleagues nationwide were texting her with messages like, “The last 3 months of your Instagram posts just got deleted!” and “Dude, you've been hacked!”
In short, the hackers wreaked havoc on Chalene's social media accounts — causing many of her followers to click the dreaded “unfollow” button. As Chalene said in her first podcast on the subject, she instantly “felt sheer panic” and “out of control.”
Chalene says the scariest truth about what happened to her is “my story could be your story.”
How the hackers got into Chalene's accounts
Believe it or not, weak passwords weren’t the culprits.
Chalene's accounts were compromised from a blend of data mining, phishing and social engineering.
The hackers guessed the answers to her security questions. How? From things Chalene and her friends and family posted online — such as those silly Facebook quizzes like “50 things you don't know about me” and “Which Harry Potter character are you?” Phishing teams sometimes develop these quizzes to get the answers to the security questions many websites use to give you access to your accounts in the event you lose or forget your password.
Think about the last time you did one of those quizzes, maybe a quiz that helped you figure out your “stripper name.” You've probably seen that one and giggled as you learned that your first name is the street you grew up on, and your last name is the name of your childhood pet. Guess what, friends? Those are two actual security questions used on banking sites!
Maybe your parents like to post childhood photos of you, tagged with your maiden name. Bingo! That’s another data source that hackers can mine for sinister purposes.
Chalene stresses that passwords and security questions are no longer enough to protect you.
The frightening truth about cyber crime
“The best defense is a good offense.” ~ Chalene Johnson
Like many victims of cyber crimes, Chalene discovered that law enforcement’s ability to help was limited. She says it was sobering to learn that the FBI and other law enforcement agencies simply don’t have the time, resources or manpower to investigate all the cyber crimes that occur each day. It was left largely to Chalene and her team to get to the bottom of the crime.
“We pretty much narrowed it down to two high school kids in different parts of the United States, and we were able to do far more intel, and far more investigative work as a team, than even the FBI was,” she says.
So what can we do to protect our social media and other online accounts? “The best defense is a good offense,” Chalene emphasizes.
Four layers of online security
Chalene now uses four layers for her own online security, and recommends others do the same to protect their accounts.
1. Two-factor authentication
The first layer of security is known as two-factor or two-step authentication. In a nutshell, two-step authentication requires you to verify your login information with another element besides your password. This second element should be something only you know.
Pro tip: If you have a GoDaddy account, learn how to lock it down with two-step authentication.
2. Security software
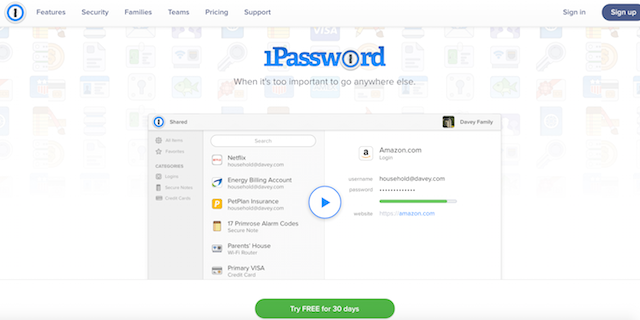
The second layer of protection is to use security software that randomizes your security answers in place of using real answers that someone can mine for data. Chalene recommends these five security software products:
Chalene personally uses 1Password because out of all the research she did, it rated the highest. And, regarding the free vs. premium versions of these software options, Chalene advises opting for the paid version. Why? She says:
“If you take security seriously … if it would be a pain in the butt to you to lose access to your bank accounts or your social media accounts … pay for the premium. It's cheap. It's like $60 a year. Who wouldn't pay that?”
3. Change passwords often
The third layer is to change your passwords routinely. Chalene acknowledges that this might be inconvenient, but it's not nearly as inconvenient as losing access to your accounts!
Be wary of WiFi
Finally, be careful using public WiFi. If you must use public WiFi, Chalene recommends setting up a VPN or virtual private network to at least encrypt anything you're putting out there.
Bonus layer: Chalene also suggests being more paranoid than you likely are. Yes, it's easy to forget that people are out there working day in and day out to access information, but you must keep your guard up to protect yourself. She says it's critical you educate yourself, do your research, and put security systems in place.