In an age where personal digital information has become the new currency, protecting your personal data from cyber criminals has never been more critical. Among the many methods these digital thieves employ, one technique, known as phishing, is particularly insidious.
What exactly is phishing, how does it pose a threat to you, and more importantly, how can you shield yourself from falling prey? In this guide, we shed light on everything you need to know about phishing attacks and provide pragmatic steps to boost your defenses.
Ready? Let’s jump in.
Disclaimer: This content is provided for informational purposes only, and should not be construed as legal advice from GoDaddy on any subject matter.
Understanding phishing
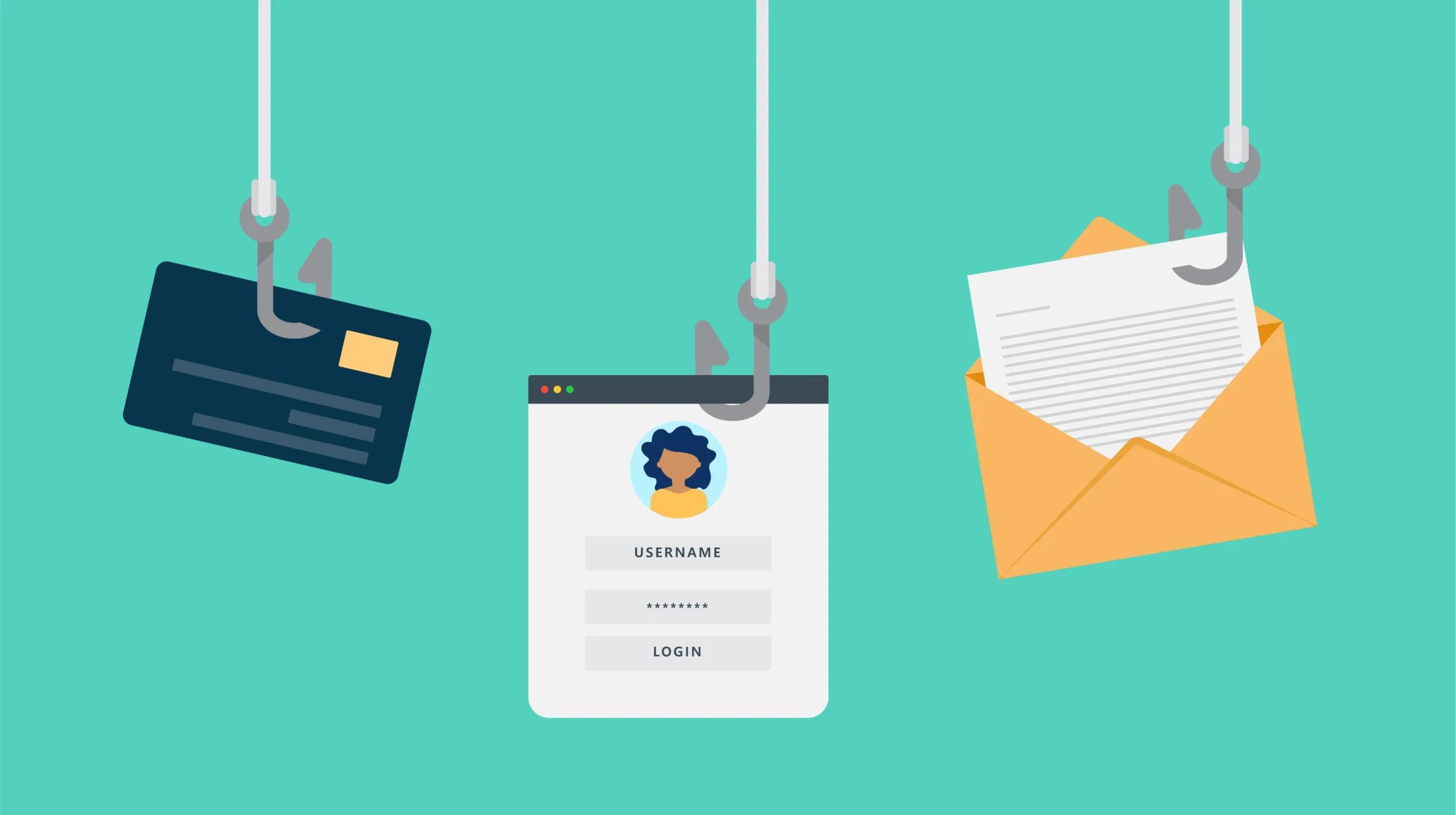
Phishing is a form of cyber fraud that involves luring internet users into revealing sensitive personal information — such as login credentials and financial information — under the guise of legitimate requests or messages. Typically, this manipulative tactic is employed via deceptive emails, texts, websites, or even instant messages.
The term “phishing” is believed to have been coined around 1996, aligning with the early advent of digital communication. This infamous technique has since evolved massively, keeping pace with technological advancements. From simplistic email frauds resembling official communications to sophisticated schemes such as spear phishing and whaling, phishing continues to change and grow as technology evolves.
Phishing is rampant. The FBI's Internet Crime Complaint Center compiled a report for 2023 showing that phishing was the most common type of cybercrime in the world, and it's continuing to accelerate. According to the report, phishing schemes accounted for more than 300,000 victims and $52 million stolen from this type of cybercrime alone.
Phishing thrives on two main psychological principles: urgency and familiarity.
By creating a sense of panic or immediate action — for example, warning you about suspicious activity on your bank account — phishers induce users into acting without proper scrutiny.
In addition, by impersonating familiar entities such as your bank or a popular online platform, phishers exploit your trust to extract sensitive information. This psychological manipulation is why phishing remains a successful and preferred method of cybercrime.
Related: Your cybersecurity nightmare — A day of shocking online hacks
Types of phishing attacks

The craft of deception is at the heart of phishing, and the sheer variety of phishing methods only shows how adaptive cyber criminals can be with their tactics. In order to fully understand the risks and the forms phishing attacks can take, it's essential to familiarize yourself with each type. Let’s take a closer look at each below.
1. Email phishing
This is the most common form of phishing, where fraudsters send out deceptive emails that impersonate trusted entities to a large pool of recipients. The purpose is to trick users into clicking on a link, downloading an attachment, or providing sensitive information.
2. Social media phishing
Increasingly popular with the rise of social media, this method involves sending fraudulent messages or creating fake profiles on platforms like Facebook, TikTok, or Instagram. Victims might be led to believe they've won a prize, their account is compromised/locked, or they might be enticed by false exclusive offers.
For a deeper look at one such phishing scam occurring with Meta business accounts, check out this report for examples.
3. Spear phishing
This is a more targeted approach where the threat actor tailors the attack towards specific individuals or companies. The emails appear to be from known contacts or corporate entities, increasing the chances of a successful exploit.
4. Whaling
Here, the big fish or “whales” of an entity, like CEOs or executives, are targeted. Given the influential roles these individuals occupy, the payoff for a successful whaling attack can be massive.
5. Smishing and Vishing
“Smishing” or SMS phishing involves fraudulent messages sent via text, while “vishing” or voice phishing includes deceitful phone calls or voicemails. Both methods exploit the perceived trustworthiness of more personal communication methods.
6. Pharming
Unlike most methods which require an action from the user, pharming reroutes users to malicious websites even if they've entered the correct address. This is done by manipulating the Domain Name System (DNS) servers or infecting the victim's computer with malware.
Related: Demystifying DNS abuse — Understanding the digital threat landscape
7. Clone phishing
In this method, a legitimate and previously delivered email is cloned or duplicated but with malicious content. The email appears to come from the original sender and seems like a resend or update of the original message.
8. Snowshoeing
This technique involves distributing spam across several domains and IP addresses to evade reputation-based spam filters. Think of it as spammer footprints being distributed over a wide area, akin to an individual walking in snowshoes to avoid sinking into the snow.
How to recognize phishing attacks

Mastering the art of recognizing phishing attacks can help to reduce your vulnerability to cyber fraud. Phishing attacks often display certain telltale signs that, once known, can act as early warning flags. These alerts take different forms, whether in the headers of a seemingly harmless email, the oddity in a website URL, or an unsolicited and urgent request for vital information.
Phishing emails and messages often exhibit a certain set of behaviors. They may contain generic greetings, grammar and spelling errors, or claim urgent action is required. Often, the sender’s address seems suspiciously similar to, but not exactly like, a legitimate email address.
The urgency of the message is usually used to scare you into action and thus deter you from taking the time to check the validity of the message you’ve received.
Additionally, inaccuracies or alterations in website URLs can be a warning sign of a phishing attack. Common tactics include swapping or dropping letters (e.g., “facebok” instead of “facebook”) or using a subdomain to give the illusion of a safe site. Always check the URL carefully, especially before entering sensitive information.
Another telltale sign of phishing attacks is requests for your personal or financial information. Legitimate organizations seldom ask for your personal, financial, or login details through an email, message or pop-up. As such, any request for critical information should be treated with extreme caution. If in doubt, directly contact the organization without using any provided links or contact information in the suspect message.
How to protect yourself from phishing attacks
Although phishing attacks are intricate and can appear legitimate, there are numerous effective strategies to help insulate yourself from them. Adopting a proactively defensive stance, backed by both knowledge and the right tools, can significantly minimize the risk of becoming a victim. Here are some practical measures you can take to beef up your defenses.
1. Be wary of unsolicited messages
Always exercise caution with unsolicited communications, especially those prompting you to act urgently or asking for personal or financial details. If you receive a suspect email, do not click on any links or download any attachments. Instead, independently verify the message contents by accessing the supposed source's website directly.
2. Always check URLs
Always verify website URLs before entering your credentials or any sensitive information. Look for “https” at the start of the URL, as the “s” denotes a secure website. Also, remember that a padlock icon next to the URL does not guarantee security — it only means that the data you send to the site is encrypted. Be sure to click on the padlock to view the security details for the site that you’re viewing.
3. Keep your antivirus active/up-to-date
Use security software to safeguard your devices. Regularly updated antivirus software can protect you against malware, ransomware, and other malicious threats. Also, regularly updating your operating system and applications allows you to benefit from the latest security patches.
4. Use 2-factor authentication whenever possible
Two-Factor Authentication (2FA) adds an extra layer of security to your online accounts and can be effective in protecting you from phishing attacks. Even if a cybercriminal successfully deceives you into revealing your credentials, they'd still need the second verification step, which is usually something in your possession like a smartphone, to gain access. This two-step process makes it significantly more challenging for attackers, providing an added layer of phishing defense.
5. Keep an eye out when using social media
Be cautious on social media. Do not accept friend or follow requests from unknown individuals and always double-check friend requests from known contacts — it might be a cloned account. Be wary of clicking on shortened links, as they can lead to malicious websites.
6. Stay educated
One of the best defenses against phishing attacks is education. Regular training via cybersecurity awareness programs can help you stay ahead of the latest phishing techniques.
Conclusion
Phishing is a pervasive threat, tricking innocent users into disclosing sensitive personal information through various disguised tactics. However, by understanding the nature of phishing techniques, being able to recognize the warning signs, as well as adopting defensive strategies, you can fortify your digital fortress against this insidious form of cyberattack.