A great-looking, high-performing website can be the key to success online, and WordPress checks all the boxes. It's almost infinitely scalable and capable of nearly endless functionality. However, as with any website, WordPress requires security measures to keep it online and running at its best.
This WordPress security guide will teach you how to thwart bad actors seeking to exploit the website you so lovingly crafted. Implement the strategies included here, and you'll likely leave hackers and attackers looking for an easier target.
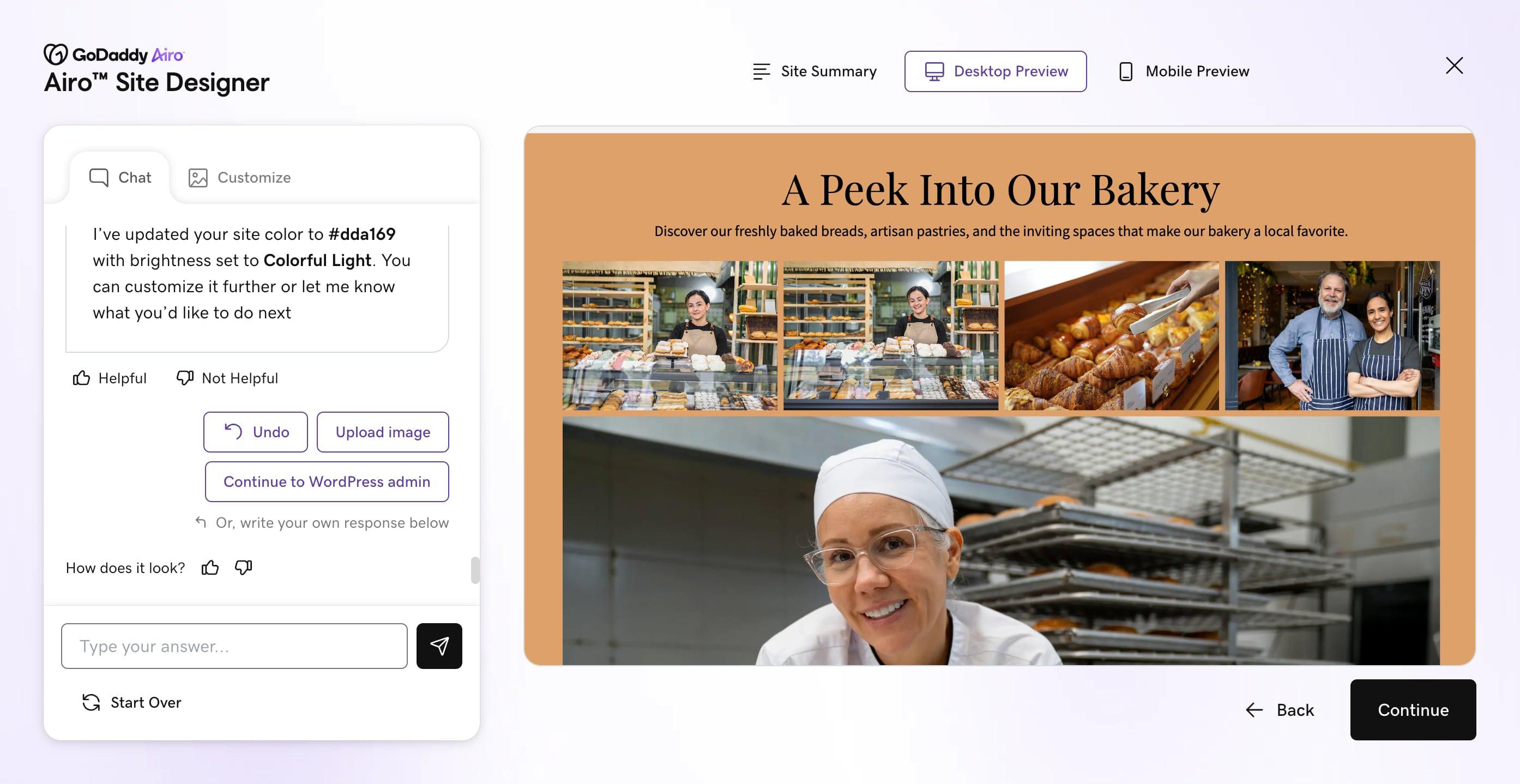
Launch your business in minutes with GoDaddy Airo®
Quick navigation
Ready to dive in? Here's what we'll cover:
- Is WordPress a secure platform?
- Why you need to secure your WordPress website
- How to secure WordPress
- Security plugins
- Security best practices
- How to identify vulnerabilities how to prevent them
- How to run a security scan
- Smart 404 blocking system
- Importance of strong passwords and two-factor authentication
- Importance of limiting the number of WordPress users and admins
- GoDaddy’s Managed WordPress Hosting service
Is WordPress a secure platform? Are WordPress websites vulnerable to attacks?
WordPress is backed by a large, active community focused on improving security. A dedicated Security Team made up of experienced developers and researchers works continuously to identify risks and release fixes. Updates follow a consistent schedule, and clear best practices exist for developers building themes and plugins.
The platform now includes stronger default protections, and common security practices are widely understood by site owners. This makes it easier to build and maintain a secure site without advanced technical knowledge.
WordPress powers more than 43% of the web and has been in continuous development for over 20 years. Its Security Team includes experts who actively monitor threats and address vulnerabilities, including those outlined in the OWASP Top Ten, a widely recognized framework for web application risks.
If you’d like to keep track of the security measures and updates in WordPress, check out the security section of their blog.
However, website security still requires attention and action. Regularly update your core software, themes, and plugins, and stay informed about new developments. Consistent maintenance is what keeps a WordPress site reliable over time.
Why you need to secure your WordPress website
Even if you’re only dabbling with WordPress, your site can still be a target for hacks and attacks. Hackers don’t focus only on large brands; they look for easy entry points, and any unprotected site can be an opportunity.
Imagine sending friends and family to that WordPress website you’re so proud of building, only to find your pages displaying odd messages for prescription medication or online gambling. That’s called SEO spam, and it’s one of the most common types of infection.
The stakes get higher if your site supports a business. If you store customer information, such as payment details or personal data, a security breach can lead to financial loss, legal issues, and reputational damage.
The good news is that securing your WordPress site doesn’t have to be complicated. A few consistent steps can make a meaningful difference in reducing risk.
How to secure WordPress
Securing a WordPress website is achievable through a combination of software applications and your own best practices. But keep in mind, even the most advanced WordPress plugin won’t save you if your security posture is lax. Similarly, even the strongest, security-first mindset could use a little reinforcement from technology.
In this section, we’ll explore WordPress security plugins, as well as best practices you should employ to keep your site secure.
Security plugins
A WordPress security plugin is a tool that helps protect your website from threats like malware, unauthorized access, and vulnerabilities. It works in the background to monitor activity, block suspicious behavior, and strengthen your site’s overall security without requiring advanced technical skills.
For the new WordPress user, you probably ask yourself, “Do I need a WordPress security plugin?” The answer is a resounding “YES,” especially if you’re not code-savvy enough to tackle the Hardening WordPress section of the WordPress Codex.
Security is a big deal. WordPress security plugins help you protect your investment of time and money to create your website.
If you don’t protect your investment, you risk losing parts — or all — of your website. Whether it is a website geared toward selling items online, or an informational website to get people to come to your brick-and-mortar location, it needs to be up to help you succeed in your online endeavor.
Features to look for in WordPress security plugins
Before reviewing some of the top WordPress security plugins, you really need to understand the features that you want to look for when choosing the right security plugins to lock down your WordPress site. Plugins should:
- Include a reliable malware scanner: A good plugin scans for a wide range of threats and flags anything that does not belong. Limited scanning leaves gaps that attackers can exploit.
- Offer a web application firewall (WAF): A firewall helps block malicious traffic before it reaches your site. This reduces the risk of bot attacks, downtime, and unnecessary strain on your server.
- Support stronger login security: Features like two-factor authentication and login protection help prevent unauthorized access. Clear guidance on password strength is also a plus.
- Provide file repair or restoration tools: You probably don’t have time to remove malware from your site files. The ability to detect changed files and restore them to a clean version can save time and reduce risk after a compromise.
- Monitor your site’s reputation: Some plugins check your site against Google’s Safe Browsing list. This helps you catch issues early before they impact traffic or visibility. Google actually labels websites that have been found with malicious hacks or suspicious content.
- Stay updated and compatible: Choose a plugin that is actively maintained and works with your current version of WordPress. Outdated tools can create more risk than protection.
Recommended WordPress security plugins
Below are five of the best WordPress security plugins available. Some of these can be stacked together, but others should be used alone. It’s important to read each plugin’s description and review its features to pick one you’re comfortable with. We’ll go over:
- Sucuri Security
- Wordfence
- iThemes Security
- Shield Security
- All In One WP Security Firewall
As a note, all of the plugins discussed below have hundreds of thousands of users who have attested to their trustworthiness.
**The features and information listed below were verified to be correct at the time of publication.*
Sucuri Security
Sucuri Security is a highly popular WordPress security plugin that:
- Monitors user activity
- Monitors files and if they’ve been changed
- Has hardening settings to block bots from adding malicious files to your site
- Offers a website firewall for premium users (paid upgrade)
- Has blocklist monitoring in case you’ve been blocklisted from places like Google, McAfee, Norton, and more
Wordfence
Wordfence has more than 5 million active installs worldwide. This plugin offers a strong premium Web Application Firewall (additional purchase required), and:
- Blocks bad bots and fake Googlebots
- IP or country blocking (paid feature)
- Live monitoring or real-time blocking
- Options to throttle or block users or bots in ways that may be suspicious or a potential risk to your website
- Two-factor authentication
- Requires users to create strong passwords
- Brute force login security
- Scans files against WordPress core files, WordPress themes, and WordPress plugins
- Is located at WordPress.org
- Scans for malicious code like trojans, backdoors, and more
- Supports WordPress multisite
iThemes Security
iThemes Security, formerly known as Better WordPress Security, was created by combining features from multiple WordPress security plugins into a single plugin. The intention was to prevent having to stack myriad WordPress plugins while providing a means for the WordPress user to go through a security checklist. This plugin offers:
- Security checks and a setup wizard
- Brute force protection
- Two-factor authentication
- File change detection
- Database backups
- User activity logging
- Strong password enforcement
- Lockout notifications
Shield Security
Shield Security offers a variety of features for securing and hardening WordPress websites, such as:
- Two-factor authentication
- Renaming WordPress login URL
- Brute force protection
- File integrity checking
- User monitoring
- Email reporting
- Firewall
- User management
- Help with reducing comment spam
- Hack protection
- Auto-repairing compromised files for WordPress core and plugins or themes from WordPress.org
- IP manager
- Lockdown on areas like hiding WordPress version, blocking XML-RPC, preventing file editing, and more
All in One WP Security Firewall
All in One WP Security Firewall is designed with many of the same features as iThemes Security. Some web hosting and plugin setups cannot handle iThemes, but might be able to handle All In One. Install and test each plugin to see what works best for you.
In the end, the important thing is to choose a WordPress security plugin that actually works!
These are just a handful of the great WordPress security plugins available to help protect your website. Do your research, pick one or more security plugins to try, and start taking a more proactive approach to WordPress website security.
Security best practices
While the plugins listed above can go a long way in securing your WordPress website, they’re by no means the only measures to implement. Your behavior and habits are just as important (if not more important) in keeping a site secure, so let’s explore best practices for keeping bad actors away from your WordPress site.
Get behind a website application firewall (WAF)
A WAF protects your website by comparing incoming traffic to a database of known bad actors. This database is continually updated, so you get protection against emerging threats. With a WAF in place, your WordPress site is less likely to fall victim to attacks such as Distributed Denial-of-Service (DDoS) and malware.
Update core files, plugins, and themes
WordPress updates almost always include security patches, which are one of the most important steps in protecting your site. Luckily, the process is quick and simple. Log in to your wp-admin dashboard, hover over Dashboard in the sidebar, then click Updates from the dropdown menu.
From there, select everything listed and run the updates. You can simplify this even further by enabling automatic updates for core files, plugins, and themes. Many managed WordPress hosting solutions include this by default, and you can also turn on plugin auto-updates directly from the Plugins section in wp-admin.
Auto plugin updates are crucial because WordPress releases security fixes through dedicated bugfix updates. Only the latest version receives full support, but critical fixes are often backported to older versions as a courtesy. These fixes are delivered automatically when auto-updates are enabled. This means your site can still receive protection against serious vulnerabilities even if you are not running the latest version.
Keeping auto-updates enabled helps ensure your site receives critical patches as soon as they are available, without relying on manual updates.
If you prefer more control, you can also enable automatic updates manually by adding this code to your wp-config.php file:
> // Enable automatic updates for all
> define(`WP_AUTO_UPDATE_CORE`, true);
> add_filter(`auto_update_plugin`, `__return_true`);
> add_filter(`auto_update_theme`, `__return_true`);Automatic updates can drastically change how a theme or plugin works. It might occasionally break something, but that risk may still be preferable to leaving vulnerabilities in your site.
Use a non-standard URL to log in
By default, the login page for WordPress websites usually ends with /wp-login.php or /wp-admin. While this is easy for users to remember, it also poses the risk of bots scanning for sites with these URL structures and attempting to gain unauthorized access. Fortunately, plugins like WPS Hide Login allow you to customize the URL for your login page, making it a much less attractive target.
Remove unused plugins and themes
One of the greatest features of WordPress is its ability to install and run plugins, which can improve your website's functionality. However, it’s possible to have too much of a good thing.
The quality of code across plugins and themes can vary, as some are created by businesses and others by hobbyists — and neither is perfect.
With each plugin installed on your WordPress site, the site becomes more likely to be hacked, as new vectors are created with each installation. It’s not enough to simply deactivate plugins that you aren’t using; you actually have to delete them in order to remove the vulnerable code from the server.
Removing unused items is equally important for performance and should be part of any WordPress security scan. The fewer active plugins, the safer and faster the site will run.
Install an SSL certificate
It should be painfully obvious by now that every website should have an SSL certificate. Put simply, SSL secures traffic, protects users against phishing, and can boost Google rankings.
With the certificate installed, you can change the WordPress Address and Site Address in WordPress by going to General Settings and setting the protocol to HTTPS. Click Save Changes to complete the installation.
Enforce strong passwords
While commonly used passwords like 123456 and password are easy to remember, they are also easy to guess, insecure, and pretty much guarantee that the account will be accessed by an unauthorized user.
A strong password contains a mixture of at least eight characters, punctuation, and upper- and lowercase characters.
You should never use the same password twice. It is also important that your password doesn’t include words that can be found in a dictionary or a proper noun, as they are especially prone to the appropriately named dictionary attack.
Detect and change default admin usernames
One of the most common security vulnerabilities occurs when you use the default admin username for your WordPress administrator account. Hackers specifically target this username in brute force attacks because it’s so predictable.
If your site still uses admin as a username:
- Create a new administrator account with a unique username.
- Log in with the new account.
- Delete the old admin account.
- Assign all content from the old account to the new one.
Many security plugins can automatically detect if you are using admin as a username and guide you through changing it. This significantly reduces your vulnerability to automated attacks.
Use CAPTCHA on forms
A hacker doesn’t need login access to cause problems on your site. Forms can become an easy entry point for spam, abuse, and even malicious activity.
CAPTCHA, short for “Completely Automated Public Turing test to tell Computers and Humans Apart,” is a tool that verifies whether a visitor is a real person. It typically works by asking users to complete a simple task, like selecting images or checking a box.
If your WordPress site has a contact form without CAPTCHA, it can be used to send large volumes of spam or malicious emails through your server. This can impact your site’s performance and damage your reputation.
Adding CAPTCHA to your forms helps block automated bots, reduce spam submissions, and protect your site. It can also help prevent brute force attacks by limiting repeated login attempts from malicious scripts.
Limit login attempts
The plugin Limit Login Attempts will keep your admin page protected with a customizable limit on the number of failed logins allowed before a user is blocked from submitting the login form. You can also add an allowlist in case a user forgets their password.
Some hosting providers already offer this as a built-in feature, so it’s a good idea to do your research before attempting the installation.
Turn off file editing
You might notice WordPress allows you to edit your theme and plugin files directly from the admin panel. This exposes a vital vulnerability that can have unintended consequences.
It’s best to disable it to prevent hackers or other users from intentionally or otherwise defacing the site. You can do this through a simple change to your wp-config.php file. Just add this to the file on its own line:
> // Disable file editing
> define(`DISALLOW_FILE_EDIT`, true);Change security keys
The security keys stored in your wp-config.php file encrypt login sessions stored in your cookies. Changing these keys will invalidate all sessions, log all users out of the dashboard, and prevent hackers from hijacking open sessions.
Changing these keys is as simple as copying and pasting. First, use the WordPress security key generator API to get your new secret keys, and then copy them. You’ll find a block of code that looks similar, which you can replace with the new block that you have copied. It will look like this:
> define(`AUTH_KEY`, `HeW#zltmGurr@u{B97hDiOr;3@<1>-^bbtua-:bC&K4`]*r 6V<-s-GtTq?lLL|h`);
> define(`SECURE_AUTH_KEY`, `B >t.QYHTKXRv/)ewR 5$iswZrLM}kAE#15?:2lu]zPd!KuB78?4fopw3QsHtx#4`);
> define(`LOGGED_IN_KEY`, `gI:T2,v7|E[.Q&[yGK|$a+s1;&$8-[?|6dE+FX|9|Ex|N[EPiQ0YzoXas=.7`4;&`);
> define(`NONCE_KEY`, `Z_-$xVrv0+VqtoVl#8|s/zeOlm^h# zHh(3me1X/S(l[(h;-+KI&cyDuLbm<!DR.`);
> define(`AUTH_SALT`, `-~i[ahut&xhfTLlnk+u^[GC2?:324X/Lo*<i{|K75j)6HI<y1<Vc$|(,-xZ+{ O]`);
> define(`SECURE_AUTH_SALT`, `B|M9s9a*iwp44|ldOHJlG9.#-Hb$t?kY|st;D9 )]FALOWt[/fYrtanxrjoxfD(z`);
> define(`LOGGED_IN_SALT`, `z_ Drd6Rip3upj:P*|2UsToIkVtaG|Nk3JKO yNq=xQZpVy7u!d@.TO8P:b5#s*H`);
> define(`NONCE_SALT`, `5/af{*Wq82Gzq56&$b)<]X=-3#NW3x++~ D|PD-oCs=(#_y-~Z=w[]W9#jBfgJ *`);Secure core files with an .htaccess
Using the .htaccess file is one of the most effective ways to improve WordPress security. It gives you direct control over how your server handles requests, which can help block unwanted access.
Start by restricting access to core WordPress files. These files are not meant to be viewed in a browser, and attempts to access them are often a sign of someone looking for vulnerabilities.
You can quickly add an extra layer of protection by placing a small block of code in your .htaccess file. Add it before or after the # BEGIN WordPress and # END WordPress tags:
> # Block the include-only files.
> RewriteEngine On
> RewriteBase /
> RewriteRule ^wp-admin/includes/ - [F,L]
> RewriteRule !^wp-includes/ - [S=3]
> RewriteRule ^wp-includes/[^/]+.php$ - [F,L]
> RewriteRule ^wp-includes/js/tinymce/langs/.+.php - [F,L]
> RewriteRule ^wp-includes/theme-compat/ - [F,L]Disable XML-RPC
Most WordPress users don’t use the XML-RPC functionality, which lets you create blog posts and interact with certain plugins. This type of functionality is helpful if you have an automated feed that posts new content to the site, but it’s highly sophisticated and rarely used.
In most cases, the best thing to do is to disable it to deny hackers a way to brute-force user passwords. In order to disable it, you’ll just need to add another block of code to your .htaccess file:
> #disable xmlrpc
> order allow,deny
> deny from allAudit file permissions
According to WordPress, developers and admins should avoid 777 file permissions at all costs. Holding files with this type of permission allows anyone on the machine to read, write, and execute any file with 777 permissions.
WordPress suggests using 755 permissions for folders and 644 permissions for files instead.
Because WordPress files are constantly updated, changed, and added to, regularly audit the website files for bad permissions to maintain a secure environment.
If you want to quickly run an audit, you can run this command from SSH to view all files in the current working directory that do not follow the WordPress guidelines for file permissions:
> find . -type f ! -perm 0644; find . -type d ! -perm 0755Disable PHP error reporting
Disabling PHP error reporting prevents hackers from gaining vital information about your website and its environment.
A common hacking technique is to view a file that displays an error to identify the operating system, the website path on the server, and even which applications are running.
As an example, suppose you access a file on the website that returns this error:
> Warning: Cannot modify header information – headers already sent by (output started at /home/jchilcher/public_html/wp-content/plugins/twitter-profile-field/twitter-profile-field.php:28) in /home/jchilcher/public_html/wp-includes/option.php on line 571.This error tells me the server is using Linux with cPanel — the main domain for this cPanel account — and the website is using the twitter-profile-field plugin. I now know where to start looking for vulnerabilities and where to exploit them.
The fix to this problem is as easy as the rest. Create or modify the php.ini file for the site and ensure that the display_errors directive is off. You can do this by adding the line:
> display_errors = OffOnce your settings have taken effect, any error that would normally display on a page will be gone.
Have a backup plan
The most important yet neglected task involved with WordPress security is having a backup plan. If the worst-case scenario becomes a reality and your website becomes a host to malware, you should already have a plan for how you will get the website back.
In most cases, those who refuse to regularly back up their sites end up regretting it. Without a clean backup, your hacked site might never be clean again, forcing you to start all over.
How to identify and prevent vulnerabilities
WordPress often releases updates to its core files, and they usually include fixes for the latest security issues. Your installed themes and plugins will also need updates, and you’ll be notified of available new versions via your WordPress dashboard.
There are a couple of big reasons for staying on top of WordPress security updates:
- You’ll be protected against any recent threats that present a danger to your site or visitors.
- Any incompatibilities between plugins, themes, and the WordPress core are likely fixed, creating a more stable system.
In short, it just makes good sense to keep your WordPress core files, themes, and plugins up to date. However, protecting your site involves much more than simply applying updates.
You’re about to learn how to check and update your WordPress website in two steps. Before you begin, you’ll want to back up your website, in case something goes wrong and you need to restore it.
Step 1: Find the WordPress updates page
First, log in to your WordPress backend. Go to the Dashboard section, and then click Updates. This offers an at-a-glance guide for any themes, plugins, or core files that need updating.
Here, you’ll see a reminder of when you last checked for updates, along with a prompt to check again. You can also find your currently installed WordPress version and an overview of any themes or plugins that have available updates.
This is where you can reinstall the latest version of WordPress if you need to—for example, if you’ve had to migrate a site or install a backup. If you use a translated version of WordPress, you’ll also get the option to install either the U.S. version or one in your own language.
Once you’re familiar with this screen, the next step is to perform the updates.
Step 2: Update WordPress core, themes, and plugins (as necessary)
Before actually updating WordPress, there are a few important things to keep in mind. These make the whole update process run much more smoothly. Here’s what you should remember:
- Create a full backup before updating your site, in case anything goes wrong.
- If possible, update WordPress using a staging or local site first, and then migrate it once you’re happy the change has been successful.
- Update the WordPress core first, then your themes, and finally your plugins. That way, it will be easier to determine the cause of any errors.
To carry out an update, go to Dashboard and then click Updates. Take a look at what’s displayed there. Depending on what you find as you get through your WordPress security updates, you might need to get the latest version of:
- WordPress: Simply click Update Now. If you don’t see it, you’re likely running the latest version.
- Themes: If updates are available, you’ll see the information displayed under Themes. Check the appropriate boxes, then click Update Themes. You’ll be notified when it’s done, and then prompted to return to the Themes or Updates pages.
- Plugins: Check the boxes for the plugins you’d like to update, then click Update Plugins. It should only take a few moments.
Remember, you can either update everything at once or update individual items as needed. The former option is more efficient, although the latter will make it easier to figure out the cause of any sudden problems. It’s not a bad idea to perform one update at a time, testing your site in between and looking for errors or compatibility issues.
How to run a security scan
Malware is not new to WordPress, and it still makes its mark on user sites every day. This software is specifically designed to intrude on your website and gain unauthorized access to your files. It’s usually accidentally installed via a corrupted file, although certain advertisements can also contain malware.
The effects of malware are wide-ranging.
It can compromise your login data, steal personal information, create spam, or hijack your computer. Some hackers even use malware to launch DDoS attacks, so making sure your site is clean should be a top priority.
The first step is to scan your site for any pre-existing malware. While some plugins, such as Wordfence Security, include a malware scanner, there are also dedicated services you can turn to, such as GoDaddy’s Website Security, powered by Sucuri.
Next, you’ll want to eradicate the malware itself. Fortunately, most of the services we’ve mentioned will do this for you. Finally, change your passwords so you don’t get compromised again.
Smart 404 blocking system
Hackers often scan websites by requesting URLs they hope exist, such as common plugin paths, backup files, and configuration files. When those pages are not found, they generate 404 errors. A large number of these errors in a short period is usually a sign of an automated scanner, not a real visitor.
A smart 404 blocking system monitors these patterns and blocks IP addresses that cross a threshold you define. You can set how many 404 errors trigger a block, as well as the time window for those requests. A practical starting point for most sites is around 10 to 15 errors within 10 minutes. You can also enable instant blocking for highly suspicious requests, such as attempts to access /wp-config.php or /.env, which legitimate users would not request.
Before turning this on, make sure to whitelist your own IP address along with any CDN or security service IPs. This helps prevent accidental lockouts.
The main benefit is stopping reconnaissance activity early, before a vulnerability is found. It also helps reduce unnecessary server load from repeated invalid requests. Most security plugins that offer this feature include logs and simple unblocking tools, making it easier to manage false positives if they occur.
Importance of strong passwords and two-factor authentication
The process of logging into WordPress can present one of the most attractive vectors for hacks and attacks. However, a strong password paired with two-factor authentication (2FA) can mitigate much of the potential risk.
Strong passwords
The simplest website security measure you can take is to use strong, unique passwords. This means skipping your dog’s name, your kid’s name, birthdays, and common words, including the word “password.”
When creating your passwords, make sure they include:
- More than eight characters
- A mix of uppercase and lowercase letters
- At least one number
- At least one special character
You should also make sure that every password you create is unique. Do not use the same password for multiple websites or online profiles, and do not use your WordPress password for anything else, especially for a social media profile.
Two-factor authentication
Two-factor authentication is a widely used security feature that adds more protection to your accounts. Major platforms like Google and Facebook rely on it to help keep user access secure.
Essentially, 2FA is an extra layer of security.
When you log into your account, you’ll be asked to verify your identity through a second device, such as your mobile phone or a 2FA hardware key. Without that authorization, you’ll be locked out. This is vital technology for anyone who values their site’s security, and it’s easy to implement for WordPress users.
One way you can implement 2FA is the Two-Factor Authentication plugin. This tool uses the Google Authenticator app to generate passcodes on your device and is simple to set up. Some larger security plugins, like Wordfence Security and Automattic’s Jetpack, include 2FA as a premium feature.
Add emergency backup codes for 2FA
When implementing two-factor authentication, it is critical to generate emergency backup codes. These are one-time-use codes that allow you to regain access to your account if you lose your 2FA device or can’t receive authentication codes.
Most 2FA plugins allow you to generate a set of emergency codes (typically 10–12 codes) that you should:
- Print and store in a secure physical location.
- Save in an encrypted password manager.
- Never share with anyone.
- Regenerate after using any of them.
Without emergency codes, losing your 2FA device could permanently lock you out of your own website.
Importance of limiting the number of WordPress users and admins
Not every user needs full access to your site. Limiting the number of users, especially administrators, reduces risk and helps keep your site easier to manage.
This follows the principle of least privilege. Give each user only the access they need to do their job. As Michiel Heijmans, formerly of Yoast, put it:
“Contrary to popular belief, not every user accessing your WordPress instance needs to be categorized under the administrator role. Assign people to the appropriate roles, and you’ll greatly reduce your security risk.”
Types of WordPress user roles
Understanding WordPress user roles helps you assign the right level of access across your team. These are the default roles on a single WordPress site:
- Administrator: Full control over the site, including plugins, themes, users, content, menus, and settings. This role should be limited to experienced users. In multisite setups, a Super Administrator manages the entire network.
- Editor: Manages content across the site. Editors can publish, edit, and delete posts and pages, including content created by other users.
- Author: Can write, upload media, and publish their own content. Cannot manage or publish content from other users.
- Contributor: Can write content, but cannot publish it. Cannot upload media or edit/delete published content.
- Subscriber: Has the most limited access. Can manage their own profile and view content, but cannot make changes to the site.
Assigning the right roles keeps your site organized and helps prevent unnecessary access that could lead to security issues.
GoDaddy’s Managed WordPress Hosting service
Managing a WordPress site takes more than publishing content. Updates, security, performance, and backups all play a role in keeping your site running smoothly. GoDaddy managed WordPress hosting is designed to handle these essentials for you, so you can focus on growing your site.
If you want a simpler way to run a WordPress site, managed hosting offers:
- Automatic updates: Core updates are handled for you, helping keep your site secure and up to date.
- Built-in security features: Includes malware scanning and proactive monitoring to help protect against common threats.
- Daily backups and easy recovery: Restore your site quickly if something goes wrong.
- Optimized performance: Managed environments with caching help your site load faster and run more efficiently.
- User-friendly dashboard: Simplifies site management with tools designed for both beginners and experienced users.
- Staging environments: Test changes before pushing them live to reduce the risk of errors.
GoDaddy managed WordPress hosting gives you a more hands-off, reliable way to run your site, with the tools you need to stay secure and perform at your best.
Ready to dial in your WordPress security?
Now, it’s time to put these WordPress security best practices, tools, and techniques into practice. Even small improvements can make a big difference in protecting your site.
If you want a more streamlined approach, GoDaddy’s Website Security helps handle many of these tasks for you, including monitoring, malware scanning, and ongoing protection.
Managing multiple sites? The Hub by GoDaddy Pro makes it easier to stay on top of security with tools for bulk updates, backups, and site monitoring, all in one place.
Disclaimer: All known trademarks contained herein are the property of their respective owners and their inclusion does not represent any affiliation, endorsement, or sponsorship.