Running a website for your small business means you're responsible for more than just showcasing your products or services online. You're also in charge of protecting the sensitive data that your visitors and customers may share with your site. The internet is home to various security threats, with bad actors constantly looking for ways to exploit vulnerable websites.
The measures you implement are the first line of defense against these online threats. From locking down your site with secure passwords to blocking malware, taking the proper precautions isn't just a nice-to-have — it’s key to help protect your website and online business.
Whether you're running a simple website, a blog, or an ecommerce platform with user accounts, the hard truth is you can't afford to take security lightly, especially if you accept purchases or handle sensitive customer information on your website.
In this guide, we'll take a deep dive into some of the most common website threats affecting small businesses today. We'll outline tangible steps to help protect against hackers and beef up your security awareness.
Here's what we'll cover:
- Why hackers target small websites
- Impact of a hacked website
- Common website security threats
- Types of website malware
- How to improve your website security
Ready? Let’s get started.
Why hackers target small websites
Let's face it – hackers aren't just after the big fish. Small business websites are prime targets too, and for good reason.
Some cybercriminals are after financial gain, looking to steal credit card info, hold your critical data for ransom, or even mine cryptocurrencies. Others are on a mission to spread malware, using your site among thousands of others as a sneaky launching pad to infect visitors. And don't forget the data hunters – they're after the treasure trove of personal information your customers trust you with.
For many hackers, a small business website is seen as low-hanging fruit – potentially easier to crack than larger, more secure corporate sites.
Common targets for hackers
When it comes to popular website platforms targeted by hackers, WordPress sites are squarely in the crosshairs. A recent report by the GoDaddy and Sucuri malware researchers showed a whopping 95.5% of websites cleaned of malware in 2023 were built on WordPress.
Why such a massive target? Well, WordPress powers over a third of the entire internet and dominates 62.5% of the open-source CMS market. Its popularity makes it a prime punching bag for hackers.
But here's the thing — website security threats aren't always aimed at specific CMS’, big name brands or even high-profile targets. Hackers routinely use automated bots to sniff out vulnerabilities across sites of all shapes and sizes. As soon as a weakness is detected, they pounce at the opportunity regardless of how big (or small) a site is.
Impact of a hacked website
Hopefully by now, you're getting just how important website security is. But in case you need a little more convincing, let's look at a few scenarios small businesses may face when hit by cyber attacks:
1. Financial loss
According to Verizon research, 43% of data breaches involve small businesses. Due to fewer active security resources generally versus large businesses, small businesses tend to be more vulnerable overall to attacks. With the average cost per breached record estimated to be $164, a security breach can be financially devastating to businesses least able to shoulder the fallout.
2. Reputation damage
As if financial turmoil wasn't bad enough, cyberattacks can diminish your brand's reputation and credibility. Businesses of all sizes have a duty to inform customers if their personal data was exposed in a breach. And if you’ve ever been a customer whose data has been exposed, you realize how this can jeopardize business relationships.
3. Search engine blocklisting
For smaller businesses who rely on web traffic, this may be the most terrifying consequence of all — getting blocklisted by search engines and internet security companies. If your hacked site gets flagged, blocked, or downgraded, your primary source of new customers could get cut off overnight.
Common website security threats
Now that we've covered why hackers target websites and the potential fallout let's dive into the nitty-gritty of what these cybersecurity threats actually look like. Knowledge is power, and understanding these common threats is your first step in building a solid defense for your online business.
Brute force attacks
Imagine a burglar trying every key on their ring to unlock your front door. That's essentially what a brute force attack is.
Hackers use automated tools to rapidly guess your passwords, trying to break into your website's admin area or user accounts. If successful, they may be able to access sensitive information or even take control of your site.
DDoS attacks
A Distributed Denial of Service (DDoS) attack floods your website with fake traffic from many different sources at once. It’s sort of like thousands of people trying to enter a store at the same time, overwhelming the entrance so no one can get in.
This overwhelming surge can crash your server or slow it down so much that real visitors can't access your site. While you're busy dealing with the traffic overload, hackers might use this distraction to attempt other nasty activities.
Data breaches
Data breaches are the cybercrime equivalent of someone breaking into your office and rifling through your filing cabinets. Cybercriminals gain unauthorized access to the business data stored on your website - for example, customer names, credit card information, or passwords. The aftermath can include legal troubles, financial losses, and a damaged reputation.
Phishing
Phishing attacks involve stealing sensitive information by masquerading as a trustworthy brand. Attackers might create fake pages on your website or send deceptive emails from your server.
These phishing schemes trick users into revealing personal information, which can then be exploited for unauthorized access or fraud, potentially damaging your business's reputation.
According to our September survey of 600 U.S.-based website owners, just over 40% said they were somewhat confident in understanding and protecting their website against phishing. 12% said they were not very confident.
Supply chain attacks/social engineering
Just as a small business relies on various suppliers and partners, your website likely depends on third-party services. Supply chain attacks target these connections.
It's like a thief gaining access to your store by posing as a trusted delivery person. Once they're in, they can potentially access your data or alter your website without you noticing.
Plugin and theme vulnerabilities
If your website uses a platform like WordPress, you're probably using plugins to add extra features. However, outdated or poorly coded plugins can be like leaving a window open in your store. Attackers can exploit these vulnerabilities to gain access to your website.
Even the most popular plugins from trusted vendors regularly release patches to fix security problems, and if you’re not applying them then it could put your site at risk.
Malware and ransomware
Malicious code known as malware and ransomware can infect small business websites, compromising data security, stealing information, or locking systems until a ransom is paid.
Ransomware attacks can take your website down, damage your website's reputation with search engines and visitors alike, and harm your ecommerce revenue.
Types of website malware
The recent Hacked Website & Malware Threat Report from the GoDaddy Infosec and Sucuri research teams provides an eye-opening analysis of common website malware used by cybercriminals.
Here's a snapshot of some of the biggest threats making the rounds:
Backdoors
In 2023, a staggering 49% of hacked sites contained at least one backdoor. Website backdoors allow hackers to modify your site without your permission and move freely through your server undetected. They're a master key for cybercriminals and a leading cause of repeat infections.
A website backdoor may be as simple as an unauthorized admin user or a small line of code hidden somewhere in your server, so it’s really important to monitor your site often for unexpected behavior.
Malware
Found on over 47% of hacked sites last year, malware is a broad term for malicious code designed to hurt your website. This includes harmful JavaScript and PHP scripts that can redirect visitors to dangerous websites, steal your login information, or download malware onto computers.
Major malware campaigns that fall under this category include:
- SocGholish: Disguised as browser updates, this malware tricks visitors into downloading harmful programs that can lead to ransomware infections.
- Balada Injector: A sophisticated attack targeting WordPress sites, known for quickly exploiting new vulnerabilities in popular plugins.

Malware can ultimately lead to data breaches, website downtime, and financial losses if left untreated.
According to our survey, only 23% of website owners said they were somewhat confident in understanding and protecting their sites against malware like Balada Injector or SocGholish. Just over 27% said they were not very confident.
SEO spam
Over 42% of hacked websites were hit with SEO spam in 2023. SEO spam infections can pollute your site with spammy content, keywords, and redirects to shady websites.
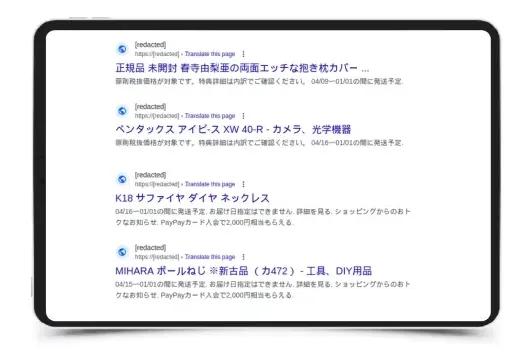
Hackers often use tricky tactics to inject bad links and code into your site, hijacking your own hard-earned search rankings for their scams. Shady affiliate marketing schemes often fuel this threat and can result in blocklisting from Google and other search engines.
According to our survey, 40% of website owners indicated that they were somewhat confident in understanding how to protect their websites against SEO spam. 17% said they were not very confident.
Hack tools
Hack tools are specialized tool kits used by attackers to exploit vulnerabilities, attack other websites, send spam, or spread malware from infected websites. GoDaddy researchers found them on nearly 11% of hacked websites last year alone.
Protecting your website from security threats
When it comes to website security, being proactive is your best defense. By implementing strong security measures from the start, you can significantly reduce the risk of falling victim to a hack. Think of it like installing a state-of-the-art security system in your home before a break-in occurs, rather than after.
Fortunately, there's good news for small business owners: you can start beefing up your defenses without breaking the bank. Let's dive into some effective measures you can implement right away:
- Backup and restore: Think of this as your safety net. Regularly backup your website and store copies in different locations. More importantly, test your restore process – you don't want to discover it doesn't work when you need it most!
- Stay updated: Keep your content management system (CMS), plugins, and themes up-to-date. It's like patching holes in your fence before intruders find them.
- Monitor your website: Keep an eye on who's poking around your site. Unusual patterns could signal a potential threat.
- Protect your admins: Restrict admin panel access, be careful who you grant admin to, and use strong, unique passwords. Consider it your website's lock and key.
- Use security plugins: Many CMS platforms offer security plugins that can add an extra layer of protection.
- Secure file uploads: If your site allows file uploads, make sure you're only accepting safe file types and scanning them for viruses.
- Less is more: Avoid installing a lot of third-party software on your website. Only use what you need, and completely uninstall plugins and themes if you’re not actively using them.
These steps are a great start, but keep in mind that each recommended step can require a significant time commitment. Professional services like GoDaddy's Website Security can be a game-changer if you're looking for more comprehensive protection that also saves you time.
This all-in-one website security solution offers several key features to keep your site safe, including:
- Regular malware scanning: With daily scans (up to twice a day), you can get help to find and tackle any malware that might be detected on your site.
- Web Application Firewall (WAF): This cloud-based service screens your real-time website traffic, helping to protect your site against threats like SQL injection and DDoS attacks.
- Content Delivery Network (CDN): A CDN helps protect your website from DDoS attacks and boosts its loading speed.
- Unlimited backups: Backups of your site can be scheduled for every 6, 12, or 24 hours and are stored for 30 days, giving you the ability to quickly restore your site in case of an accident.
- Continuous monitoring and alerts: Stay informed about your site's security status, including blocklist status, SEO spam, SSL changes, and website uptime.
- Malware cleanup: If a threat is detected, the service helps to clean up the malware, saving you time and potential headaches.
- SSL certificate: Website Security also includes an SSL certificate to keep your web traffic encrypted.
Investing in a security solution can provide peace of mind and save you time and potential headaches down the road. By taking a preventative approach with tools like these, you're not just reacting to threats – you're actively shielding your website against them.
At GoDaddy, we're committed to helping small businesses thrive online, and that includes helping keep your website secure. We offer a range of website security solutions and are here to support you on your journey to a safer online presence.
By implementing these security measures and staying informed about emerging threats, you're taking crucial steps to protect your business, your customers, and your peace of mind. After all, a secure website is the foundation of a successful online business.
Remember, you've got this – and we've got your back.
Disclaimer: This content is provided for informational purposes only, and should not be construed as legal advice from GoDaddy on any subject matter.







