1/3
Most recent stories
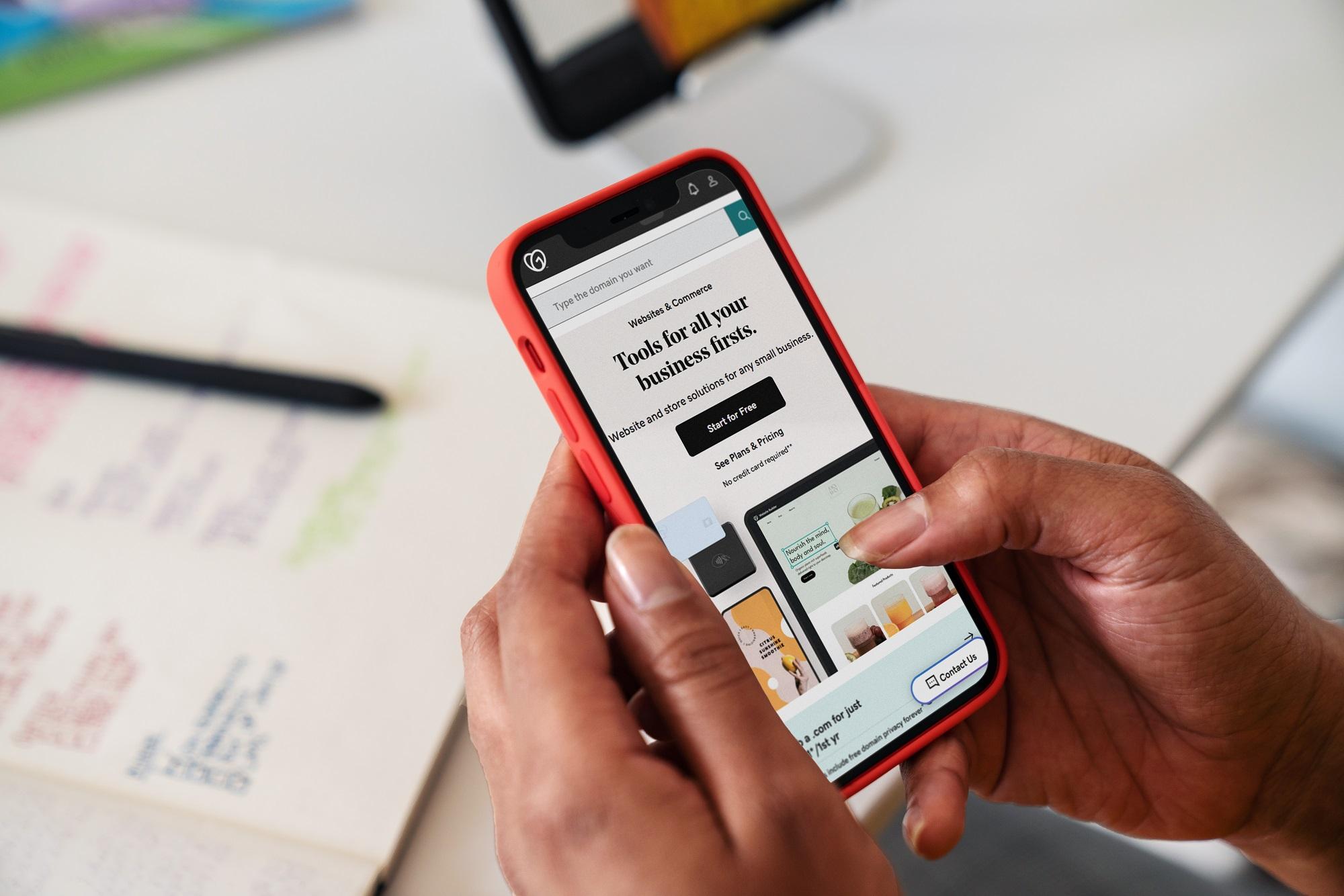
See All PostsBusinessHow to create a small business sales plan that’s bound to be successful
If you want to start your own small business, you need a small business sales plan. And like all good plans, it can’t just live in your head. It needs to be put to paper—or at least in a digital document—so it can be shared with your team. Everyone, especially current and future employees, should […]
Learn moreExplore more on marketing
This is a place for stories andnews about inspiring and
fearless people doing
interesting things.