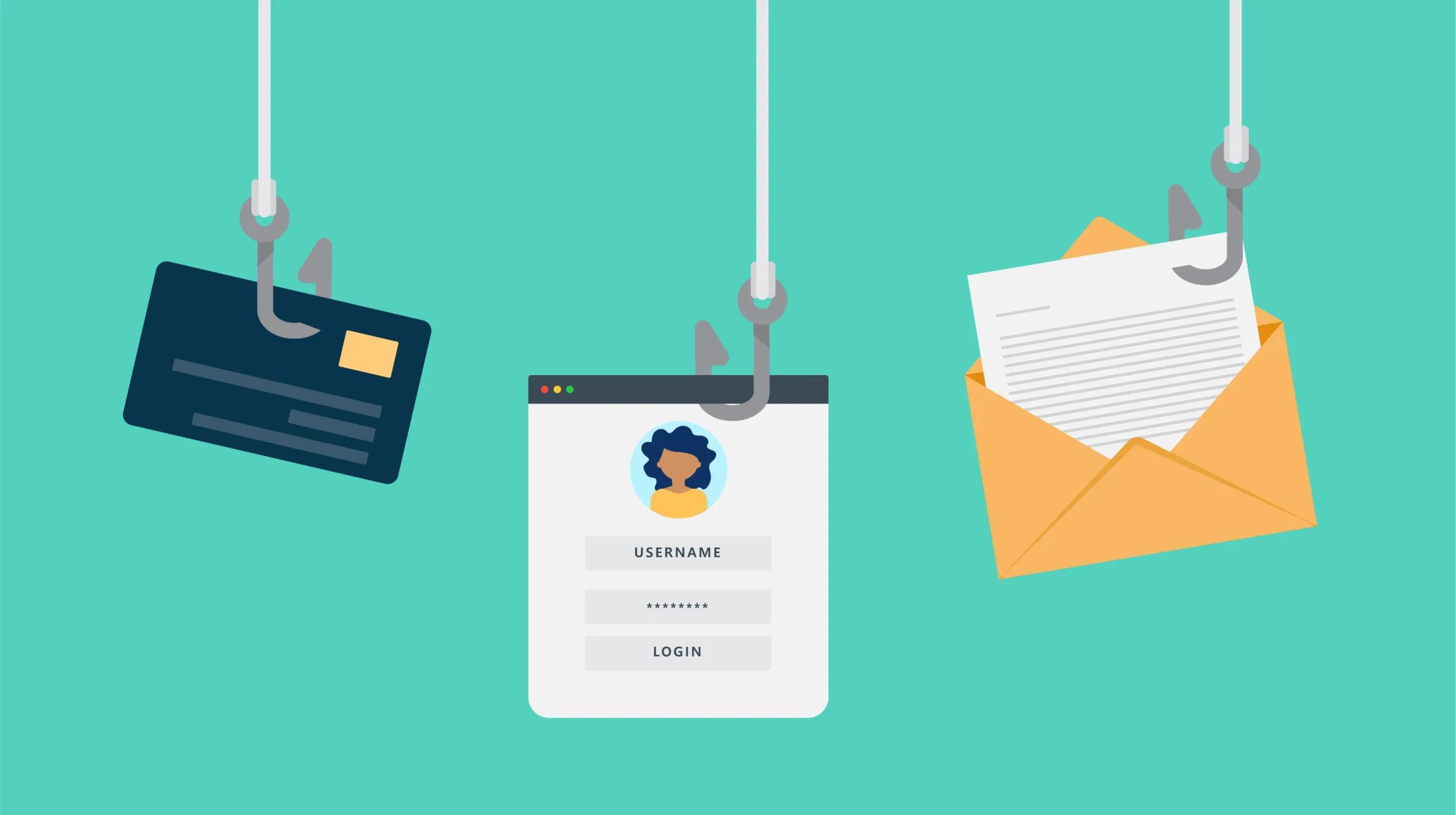
For small business websites or eCommerce websites, user registration functionality is a common need. As a result, users share sensitive information when they register for an account on a website. This could include their mailing address, email address or even credit card details. It’s a necessity, as it offers users a better website experience, but it can also leave the information vulnerable if a brute force attack occurs on your site.
Small business owners and their employees have a lot to deal with on a daily basis, so website security tends to be a low-priority concern. As a result, 43 percent of cyber attacks are directed at small businesses.
When it comes to online security vulnerabilities, brute force attacks are one of the most popular hacking methods.
Brute force attacks are used to gain backend access to a website and to get important information by cracking passwords.
This particular type of cyber attack estimated to have increased by 400 percent in 2017. To protect your small business, this article will help you understand how brute force attacks work and how to prevent them from striking your website.
Related: Understanding Online Security Threats
What is a brute force attack?

A brute force attack is when hackers use methods of trial-and-error to gain access to an authorized account. This might involve password or personal identification number (PIN) cracking, depending on the situation. Most brute force attacks are automated — so businesses of all sizes might be targeted. According to Rob Shapland, principal cyber security consultant at First Base Technologies LLP, brute force attacks are the most common and perhaps the least subtle cyber attack.
If your website lacks security and protection, attackers have an easy way in.
Brute force attacks are often used by cybercriminals to crack encrypted data to steal information to be used for fraudulent activities. (It’s worth mentioning, however, that not all brute force attacks involve malicious intent — they can also be used by security analysts to test a network’s security.)
Related: What is the cybersecurity skills gap and what does it mean for your small business?
How does a brute force attack work?
Understanding brute force attacks and how they work is not complicated — it’s protecting yourself from them that’s more challenging.
Any website with a login page (or password protection of some sort) is a potential target of this type of attack.
These content management system (CMS) admin pages are the most commonly attacked:
- WordPress wp-admin or wp-login.php login pages
- Magento /index.php or admin pages
- Joomla! administrator
- vBulletin admincp
- and other generic login pages on various websites
When an attacker wants to gain access to a website, a user account or other encrypted information, they must first do something to decrypt or unlock this information.
The process starts by trying different possible password combinations. This goes on until they successfully decrypt wherever they’re trying to get into. There are thousands of possible password combinations for a single account. The standard shortest password length is eight characters.
Many websites also impose additional requirements to add complexity to user passwords (i.e. uppercase and lowercase sensitive, alphanumeric combination, special characters). These simple guidelines can take a standard password from having thousands of possible combinations to trillions.
Of course, even all this is just a slight annoyance for a hacker with the right tools and know how. There are plenty of tools that are capable of generating thousands of possible password combinations and submitting these in a matter of seconds.
Related: 10 best practices for creating and securing stronger passwords
The motive behind brute force attacks
Brute force attacks give hackers illegal access to websites that contain valuable information (like credit card credentials). Their efforts can either shut down the website entirely or gain access to user accounts (and sensitive user information).

The GitHub brute force attack in 2013 is considered to be the largest brute force attack recorded in recent history. Many accounts were compromised: there were 40,000 hacker IP addresses involved in the attack, who primarily targeted those with weak password combinations. After the attack, GitHub urged users to set up two-factor authentication for their accounts.
In April of the same year, Cloudflare, a popular web performance and security service, blocked as many as 60 million brute-force requests on WordPress in the course of just one hour. Regardless, there were still successful brute force attack attempts against tens of thousands of websites. WordPress rolled out two-factor authentication following the attack.
How to prevent brute force attacks
The following represent the simplest precautionary measures that any user can take to help guard against brute force attacks:
- Longer password length (over the standard 8 characters)
- Uppercase and lowercase combination
- Alphanumeric password combination
- Adding special characters
- Limiting login attempts
- Using CAPTCHA
- Enabling two-factor authentication
Your next best bet?
Use powerful security tools with features to prevent brute force attacks.
These tools can deny a user (hacker) after setting a limited number of failed login attempts, which limits their effectiveness:
GoDaddy’s Website Security
Powered by Sucuri, GoDaddy’s Website Security GoDaddy’s Website Security is a powerful yet simple solution to enhance website security and reduce the risk of malware. It’s ideal for website security beginners — providing that you have a foundational level of protection in place to protect your website. This tool can protect your website from distributed denial of service (DDoS) attacks, brute force attacks, SQL injection, cross-site scripting and more.
Sucuri Security
The Sucuri Security plugin for WordPress (free) offers website security features including security activity auditing, file integrity monitoring, remote malware scanning, security hardening and security notifications. The premium version of this highly rated plugin also provides a website firewall.
Another way to protect your website is to schedule regular website backups.
Having a backup is crucial to restoring your website after a hacking attempt or accidental damage has occurred.
GoDaddy’s Website Backup service features automatic daily backups and one-click restoration.
Final thoughts
Cyber criminal activities are becoming more common and even the smallest businesses aren’t safe from them. As soon as you launch your website, you’re a target of a potential attack. So don’t wait to take action when it’s already too late — be proactive now.